Overview
Critical Insights
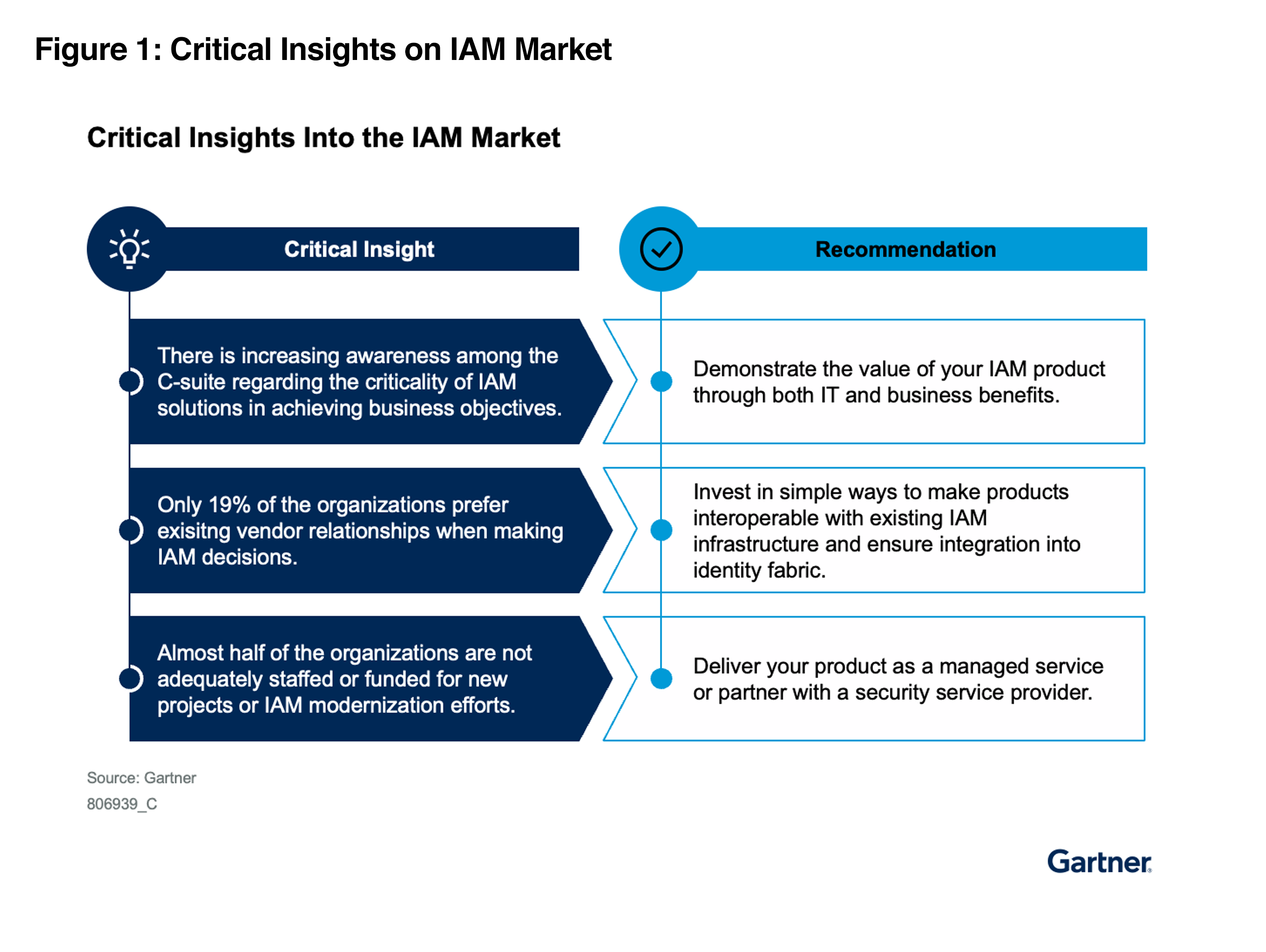
There is increasing awareness among the C-suite regarding the criticality of identity and access management (IAM) solutions in achieving business objectives. This is driving the involvement of the majority of IAM leaders (those responsible for IAM in their organizations) in decisions related to strategic business initiatives.
Only 19% of organizations prefer existing vendor relationships when making IAM investment decisions; most of the surveyed respondents are choosing disparate tools offering best capability for each use case from multiple vendors. Identity fabric principles can help address the resulting integration challenges by offering an architecture that is composable and resilient.
Almost 50% of organizations are not adequately staffed or funded for new IAM projects or IAM modernization efforts, mostly due to lack of skilled IAM personnel.
* GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
* Gartner, Emerging Tech: Identity-First Security — Position Products to Evolving IAM Goals, Swati Rakheja, Sean ONeill, 1 March 2024
* This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from ID North.